| Vulnerability Name | CVE-2023-35385, CVE-2023-36895, CVE-2023-29328 Remote Code Execution Vulnerabilities |
| Severity | CRITICAL |
| CVSS | 9.8 and 8.8 |
| Affected Products | Windows 10 and Windows 11 operating systems, MS Outlook, MS Teams |
These vulnerabilities can be exploited by malicious actors to gain unauthorised elevated access, compromise sensitive data, or disrupt normal operations through the Windows message queuing service, Microsoft Outlook and/or Microsoft Teams. Microsoft has released several updates & patches to remediate these vulnerabilities.
For ONGC customers with Managed Security Services:
We want to assure you that our expert team is proactively working to manage and remediate this vulnerability on your behalf. Our security analysts are actively monitoring the situation, and we will take the necessary steps to protect your environment from any potential exploitation. Our security team will contact you if any further action is required from you.
For ONGC customers without Managed Security Services:
We highly recommend following the recommended remediation steps outlined below to safeguard your systems and minimise any potential impact from this vulnerability.
Unsure if you have coverage? Check out our article on Managed Services vs Managed Security or contact our team to discuss available solutions.
Resolution:
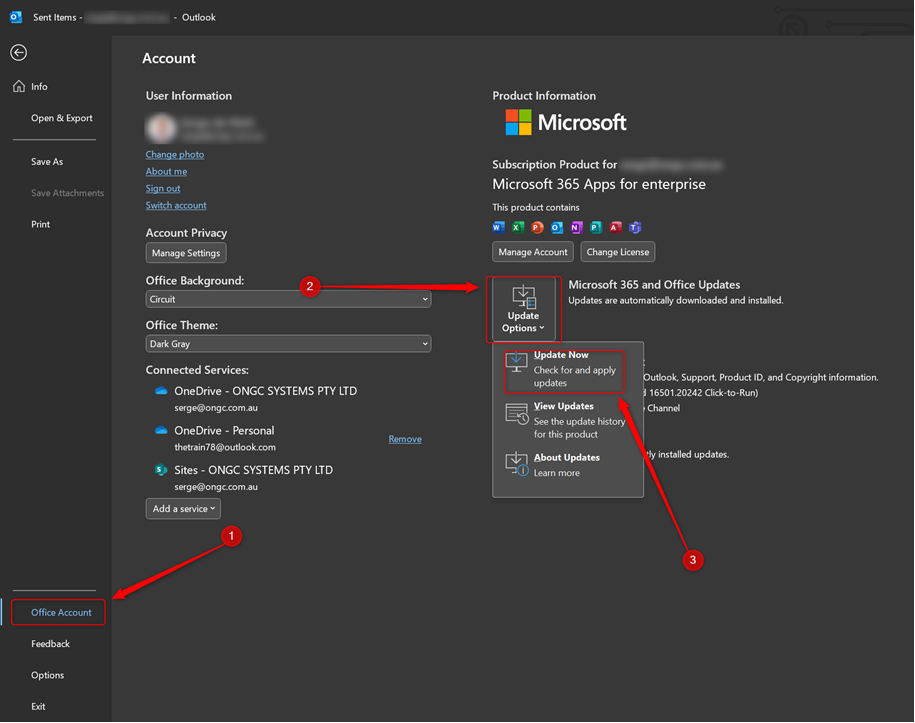
Install the latest OS security updates on your device through the Windows Update functionality. In addition, please update your Microsoft Office application by running the update functionality in any Office application. This can be found via menu File > Office Account > Update Options > Update Now